In today’s digital age, ensuring robust cybersecurity is paramount for organizations of all sizes. A critical component of achieving effective cybersecurity is implementing Governance, Risk Management, and Compliance (GRC) strategies. This guide explores the vital role of GRC in cybersecurity, examining how it strengthens governance, manages cyber risk, and helps organizations build a resilient cybersecurity posture. From understanding the core components of a GRC framework to implementing practical GRC strategies, we will explore how companies safeguard their valuable assets and maintain trust in an ever-evolving threat landscape.
Understanding GRC Cybersecurity
What is GRC Cybersecurity?
GRC stands for Governance, Risk Management, and Compliance. It is a structured approach that integrates these three critical functions within an organization to achieve strategic objectives while managing risk and meeting compliance requirements. Governance provides the framework for decision-making and accountability. Risk management involves identifying, assessing, and mitigating potential threats and vulnerabilities.
Compliance ensures adherence to regulatory requirements, industry standards, and internal policies. By integrating these functions, GRC provides a holistic view of an organization’s operations, thereby enhancing its ability to manage cyber threats and maintain effective data security. GRC solutions often include GRC software to streamline these processes and provide real-time insights.
The Importance of Governance in Cybersecurity
Governance plays a crucial role in cybersecurity by establishing clear roles and responsibilities, setting strategic direction, and ensuring accountability across the organization. Effective cybersecurity governance involves defining policies, standards, and procedures to manage cyber risk and protect valuable assets. It also entails establishing a framework for decision-making, oversight, and reporting on cybersecurity performance.
Strong governance ensures that cybersecurity is aligned with the organization’s strategic objectives and that adequate resources are allocated to manage cyber risks effectively. Through robust governance practices, organizations can strengthen their cybersecurity posture, meet compliance requirements, and better respond to evolving cybersecurity challenges. The grc achievement relies heavily on a well-defined governance structure.
The Three Pillars of Cybersecurity GRC
Effective GRC is built on three pillars: Governance, Risk Management, and Compliance. Each pillar plays a critical role in maintaining organizational resilience.
Governance in Cybersecurity
Governance serves as the strategic compass for an organization’s cybersecurity posture, providing the direction and accountability to ensure security efforts are disciplined and purposeful. This is achieved by drafting comprehensive security policies and standards and clearly defining leadership’s roles and responsibilities to ensure ownership at the highest levels. Through continuous oversight and rigorous reporting, governance provides the transparency needed to verify that all security initiatives remain strictly aligned with the broader organizational strategy and its specific risk appetite.
Risk Management in Cybersecurity
Effective risk management serves as the investigative core of a GRC strategy, focusing on systematically identifying, assessing, and mitigating potential threats before they can be exploited. This process begins with rigorous risk assessments and threat modeling to map the landscape of possibilities, followed by prioritizing high-impact risks to ensure resources are directed where they are needed most. By implementing specific mitigation strategies and technical controls, organizations move beyond a reactive firefighting mentality. When these practices are fully integrated into a GRC framework, they allow a company to proactively reduce its exposure to cyber threats and build long-term operational resilience.
Compliance in Cybersecurity
Compliance acts as the regulatory anchor of a security program, ensuring that an organization’s technical and operational practices align strictly with legal, industry, and international standards. This involves meticulous mapping of internal controls to global frameworks such as GDPR, HIPAA, ISO 27001, and NIST to ensure no requirements are overlooked. By conducting regular audits and assessments, organizations can validate their security posture and provide transparent reporting to stakeholders. Ultimately, a robust approach to compliance transcends the mere avoidance of legal fines; it serves as a powerful signal of reliability that strengthens trust with customers, partners, and regulators alike.
Implementing GRC Strategies
Key Components of an Effective GRC Strategy
An effective GRC strategy hinges on several key components that work together to bolster an organization’s cybersecurity. First and foremost, a robust risk assessment process is essential. This involves identifying potential cyber risks, evaluating their likelihood and impact, and prioritizing them by severity. Next, clear roles and responsibilities must be defined across the organization, ensuring that everyone understands their part in maintaining data security and adhering to compliance requirements.
Policies and procedures should be established to guide cybersecurity practices and provide a framework for decision-making. Additionally, implementing security controls, both technical and administrative, is critical to mitigate identified risks. A robust GRC components strategy is not static; it requires ongoing monitoring, evaluation, and adaptation to address evolving cybersecurity threats and regulatory requirements.
Steps to Implement a GRC Strategy
To successfully implement a GRC strategy, several key steps must be followed. First, conduct a comprehensive risk assessment to identify and evaluate potential cyber threats. Based on the assessment results, develop a GRC framework that aligns with the organization’s strategic objectives and risk tolerance. Next, define clear roles and responsibilities for GRC activities across different departments. Implement security controls to mitigate identified risks and ensure compliance with regulatory requirements.
It’s also crucial to establish a monitoring and reporting mechanism to track GRC performance and identify areas for improvement. Regularly review and update the GRC program to address emerging cybersecurity challenges and the evolving regulatory landscape. Robust GRC implementation requires a collaborative effort involving stakeholders across the organization’s functions.
Tools and Software for GRC
Various GRC tools and GRC software solutions are available to streamline and automate GRC processes, enhancing an organization’s cybersecurity efforts. These tools often provide features such as risk assessment, policy management, compliance tracking, and incident response. GRC platforms can help organizations centralize their GRC activities, improve visibility into their risk posture, and ensure consistent application of security controls.
Many GRC solutions also offer integration capabilities with other security and compliance systems, such as SIEM and vulnerability management tools. When selecting a GRC tool, consider scalability, ease of use, reporting capabilities, and integration options. Implementing a GRC tool can significantly improve an organization’s security compliance program’s efficiency and effectiveness, enabling it to better manage risk and meet compliance requirements. Using a GRC tool allows the GRC achievement to be achievable.
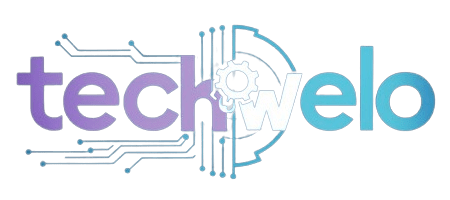
Role of GRC in Cyber Risk Management
Understanding Cyber Risk
To effectively implement GRC in cybersecurity, it is crucial to have a comprehensive understanding of cyber risk. Cyber risk encompasses any potential threat that could exploit vulnerabilities in an organization’s information security systems, leading to financial losses, reputational damage, or legal liabilities. Understanding cyber risk involves identifying potential cybersecurity threats, assessing their likelihood and impact, and prioritizing them by severity.
This understanding forms the foundation for developing Robust GRC strategies and security controls to mitigate these risks. A thorough risk assessment is a vital component of any GRC program, enabling organizations to allocate resources effectively and focus on the most critical cyber threats. This understanding must also drive the implementation of a GRC framework that effectively addresses these identified risks.
Integrating GRC with Cyber Risk Management
Integrating GRC with cyber risk management is essential to creating a unified, proactive cybersecurity approach. This integration involves aligning governance policies, risk management processes, and compliance requirements to effectively manage cyber risk. By integrating these functions, organizations can gain a holistic view of their cybersecurity posture, identify potential gaps in their defenses, and implement targeted security controls to mitigate those risks.
Robust GRC in cybersecurity ensures that cyber risk management is not treated as an isolated function but is embedded into the organization’s overall governance structure. This approach enhances accountability, improves decision-making, and enables organizations to respond more effectively to emerging cybersecurity challenges. The grc achievement hinges on seamlessly integrating these elements for robust data security.
Effective Cybersecurity Frameworks
Effective cybersecurity frameworks play a crucial role in guiding an organization’s cybersecurity efforts and ensuring alignment with industry best practices and regulatory compliance. These frameworks provide a structured approach to identifying, assessing, and managing cyber risk, as well as implementing security controls to protect valuable assets. Popular cybersecurity frameworks include the NIST Cybersecurity Framework, ISO 27001, and CIS Controls.
These frameworks offer a comprehensive set of guidelines and recommendations that organizations can adapt to their specific needs and risk profiles. Implementing a cybersecurity framework helps organizations establish a strong foundation for their security compliance program, improve their security posture, and meet compliance requirements. The use of such frameworks also supports the effective implementation of a GRC program and helps achieve GRC initiatives. Therefore, implementing a cybersecurity framework helps organizations manage risk.
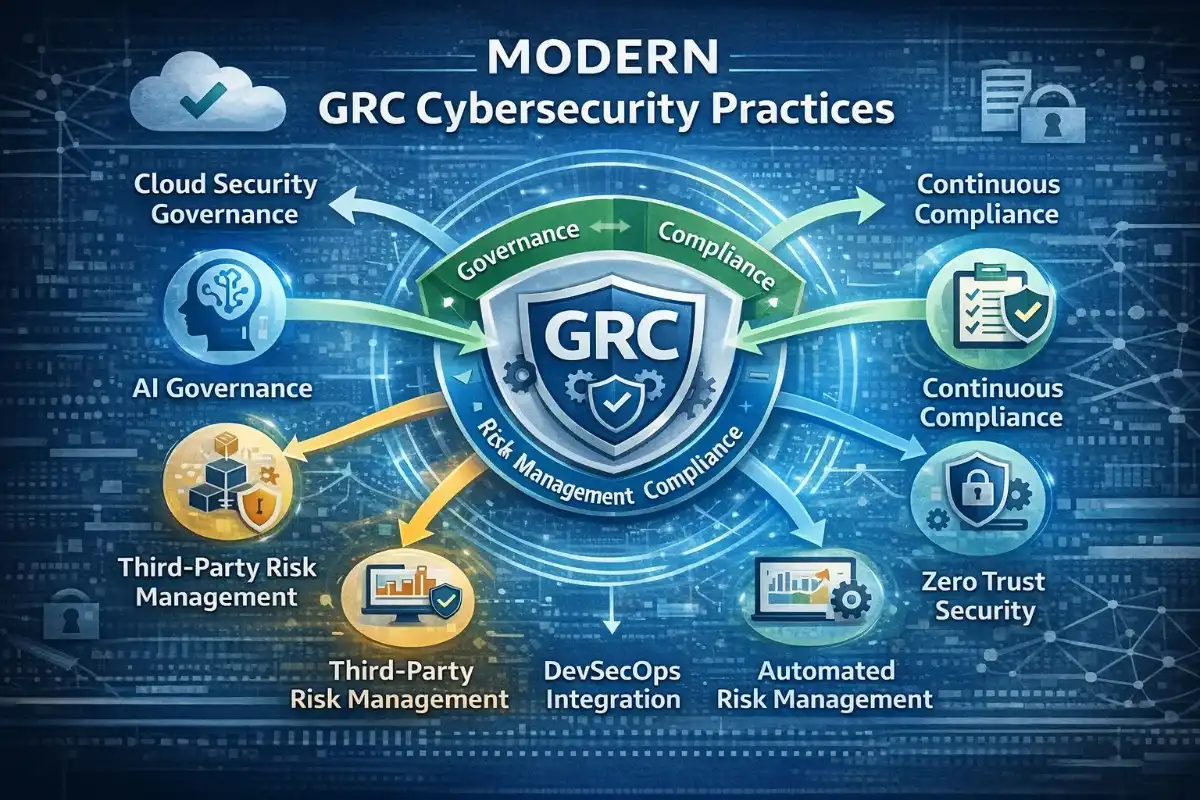
Role of GRC in Modern Security Trends
Cloud security governance
GRC ensures that cloud services are adopted securely and comply with organizational policies. It helps monitor cloud configurations and access controls to prevent data breaches.
AI governance
GRC oversees AI and machine learning systems to ensure ethical, secure, and responsible usage. It mitigates risks from biased algorithms, data misuse, or unauthorized access.
Third-party risk management
GRC identifies and reduces risks associated with vendors, suppliers, and other external partners. It ensures that third-party practices meet security and compliance standards.
Zero trust integration
GRC supports a zero-trust approach by enforcing strict identity verification for all users and devices. It reduces the chance of unauthorized access and strengthens network security.
DevSecOps alignment
GRC integrates security within the software development lifecycle, ensuring code is secure from the start. This alignment helps teams proactively manage risks while accelerating development.
Overview of Cybersecurity Challenges
Organizations today face a myriad of cybersecurity challenges, ranging from sophisticated cyber threats and data breaches to regulatory compliance requirements and evolving technological landscapes. These challenges require a proactive, comprehensive approach to cyber risk management. Cyber threats are becoming increasingly sophisticated, with attackers employing advanced techniques to exploit vulnerabilities and gain unauthorized access to sensitive information.
Regulatory requirements, such as GDPR and HIPAA, impose strict obligations on organizations to protect personal data and maintain data security. Additionally, the rapid pace of technological change introduces new security risks that organizations must address to maintain a strong cybersecurity posture. Successfully navigating these cybersecurity challenges requires a robust GRC program and effective GRC strategies.
Modern GRC Cybersecurity Practices
Emerging Trends in GRC Cybersecurity
Emerging trends in GRC for cybersecurity highlight the evolving landscape and the need for organizations to adapt their GRC programs accordingly. One key trend is the increasing integration of automation and artificial intelligence (AI) into GRC solutions. AI-powered GRC tools can enhance risk assessment processes, automate compliance monitoring, and improve incident response times. Another trend is a shift towards a more proactive, threat-centric approach to cyber risk management, with organizations focusing on identifying and mitigating potential cyber threats before they materialize.
Additionally, there’s a growing emphasis on data privacy and protection, driven by stricter regulatory requirements. Robust GRC now includes continuous monitoring and real-time reporting to ensure ongoing compliance and address cybersecurity challenges dynamically. Companies must embrace these trends to maintain strong data security and ensure the success of GRC within their organization’s cybersecurity efforts.
Case Studies of Successful GRC Implementation
Examining case studies of successful GRC implementation offers valuable insights into how organizations can effectively leverage GRC to enhance their security compliance program. A common theme among these success stories is the commitment to a strong governance framework that clearly defines roles and responsibilities. Organizations that implement GRC effectively also prioritize risk management, conducting regular risk assessments to identify and mitigate potential cyber risks.
They also leverage GRC software to automate compliance and improve visibility into their security and compliance posture. Furthermore, successful and strong GRC implementations involve ongoing training and awareness programs to ensure that all employees understand their role in maintaining data security. By learning from these case studies, other organizations can gain valuable insights into implementing a GRC strategy that bolsters their cybersecurity defenses and ensures GRC success within their environment. These examples highlight the importance of GRC in cybersecurity.
The Future of GRC in Cybersecurity
The future of GRC in cybersecurity is poised to be shaped by several key factors, including technological advancements, evolving cybersecurity threats, and increasing regulatory compliance. As organizations become more reliant on cloud computing and other emerging technologies, the need for robust GRC will become even more critical. GRC in cybersecurity will increasingly focus on automation, artificial intelligence, and machine learning to enhance risk assessment, threat detection, and incident response capabilities.
Furthermore, there will be a growing emphasis on integrating GRC with other security and compliance systems to provide a holistic view of an organization’s security posture. Organizations must also adapt their GRC framework to address emerging cyber risks, such as supply chain attacks and IoT vulnerabilities. The future of GRC in cybersecurity lies in its ability to adapt to these challenges and provide organizations with the tools and insights they need to effectively manage risk and ensure data security. The organization’s cybersecurity relies on the future of GRC in cybersecurity.
Final Thoughts
In today’s digital world, GRC is no longer optional it is a strategic necessity for organizations that want to maintain effective cybersecurity and stay competitive. By integrating governance, risk management, and compliance into a unified framework, businesses gain complete visibility into their security posture, allowing them to identify and address potential threats before they escalate.
An effective cybersecurity GRC program not only helps reduce risks but also ensures that all security initiatives align with the organization’s overall business goals. It strengthens compliance with industry regulations and standards, safeguarding the company from legal and financial penalties.
Furthermore, GRC enables organizational resilience by establishing clear processes, assigning accountability, and enabling continuous monitoring. It prepares businesses for future cybersecurity challenges, adapts to evolving threats, and supports informed decision-making. By adopting GRC, organizations can confidently manage risks, maintain trust with stakeholders, and achieve long-term security and business success.
Frequently Asked Questions (FAQs)
What is GRC in cybersecurity?
GRC in cybersecurity is the combination of governance, risk management, and compliance within an organization’s security program. It helps ensure that security efforts support business goals and regulatory requirements. By integrating these functions, organizations can proactively manage risks and maintain compliance.
Why is GRC important?
GRC is important because it aligns security strategies with overall business objectives. It helps organizations identify and reduce risks before they become incidents. Additionally, it ensures compliance with laws and regulations, protecting the organization from penalties and reputational damage.
What does a GRC analyst do?
A GRC analyst monitors potential security risks and evaluates their impact on the organization. They ensure that policies, controls, and procedures comply with regulations. They also support governance processes, helping leadership make informed decisions about cybersecurity initiatives.
What frameworks are used in GRC?
GRC frameworks provide structured approaches to managing cybersecurity risks and compliance. Common frameworks include NIST, ISO 27001, COBIT, SOC 2, and PCI DSS. Each framework helps organizations align security practices with industry standards and regulatory requirements.
How to implement GRC?
Implementing GRC starts with defining governance structures and responsibilities. Next, organizations assess risks, map compliance requirements, select a suitable framework, and implement necessary controls. Continuous monitoring and improvement ensure the program remains effective and up to date.